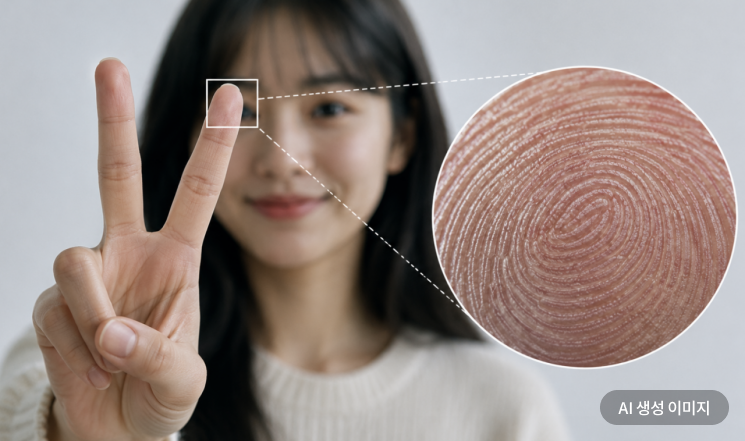
The commonly used 'V' pose when taking photos
has sparked warnings about the risk of personal information leaks.
With the advancement of artificial intelligence (AI) technology and high-resolution cameras,
it is now noted that fingerprints can potentially be reconstructed from just the fingers in a photo.
Fingerprint Reconstruction from Selfies... Possible Within 1.5 Meters
According to the South China Morning Post (SCMP) in Hong Kong,
financial expert Li Chang appeared on a Chinese television program
and demonstrated the possibility of reconstructing fingerprints using celebrity selfies.
Li Chang explained that when a finger is directly facing the camera,
photos taken within a distance of 1.5 meters
could allow for the extraction of fingerprints.
He added that even at a distance of 1.5 to 3 meters,
about half of the hand's detailed features can be reconstructed.
The program also introduced how, after enhancing photos using editing software and AI tools,
the fingerprint ridges on fingers could be revealed.

The risk of fingerprint reconstruction increases with higher resolution photos and the leakage of multiple related images showing fingers. The photos show similar images where the fingers of BLACKPINK member Jennie are visible. Jennie Instagram
원본보기 아이콘The Sharper and More Numerous the Photos, the Greater the Risk
Jing Jiu, a professor of cryptography at the University of Chinese Academy of Sciences, told Chinese media China Newsweek
that in the case of portraits taken with high-performance cameras,
even a 'scissor hand' pose
could make it possible to reconstruct detailed information about the hand.
However, Professor Jing explained that actual fingerprint reconstruction is not easy due to many variables,
including lighting, focus, and image sharpness.
Still, he pointed out that the risk may increase if more high-resolution devices are used and multiple related photos are leaked.
Risk of Financial Loss and Identity Theft if Fingerprints Are Leaked
Li Chang warned that, like facial data,
fingerprints are permanent biometric information that is difficult to change once leaked.
He explained that such leaks could lead to financial loss or identity theft.
Li Chang further recommended that before posting selfies online,
people should blur or pixelate their hands in the images.
He also advised against registering fingerprint data on devices of unclear origin.
After the program aired, the topic
spread rapidly on Chinese social networking services (SNS).
One user commented, "From now on, I guess I'll just have to make a fist in my selfies."
Another user wrote, "I should clean the fingerprint marks off my phone screen more often now."
Uploaded Finger Photo to SNS, Almost Unlocked a Door Lock
According to Chinese media Sohu News,
in July last year, a man in Hangzhou, China
uploaded a photo online with his fingers clearly visible,
which was then downloaded by a criminal group attempting to unlock a smart door lock.
However, the attempt was reportedly unsuccessful.
Meanwhile, Fei Zeyong, director of the Qianxin Industrial Security Research Center in China,
stated that even if it is technically possible to extract fingerprints from selfies,
it is not easy to use them in actual crimes.
Director Fei explained that fingerprint data is mostly exploited in environments with relatively low security,
and it is more likely to be abused for making forged documents.
He also noted that AI technology is being used to counter new types of fraud,
and that some AI tools can detect face synthesis in real time.
Our Information Could Be Sold Somewhere...
Meanwhile, as AI-based image processing technology becomes more advanced,
personal information leaks through photos are emerging as a new problem.
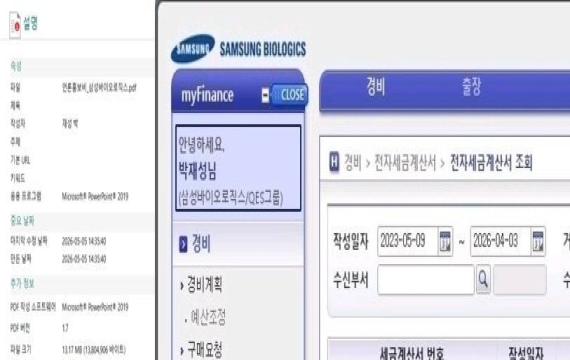
On Chinese SNS, concerns have been raised that apps like 'AI Face Reading Tests' or 'Free Palm Reading' apps
could collect or
store and misuse facial and palm biometric data.
In fact, an IT company employee in Shanghai, China, was caught
illegally collecting and storing more than 1,700 facial biometric records
via a 'beauty test' application and selling them on the dark web.









![[Reportage]"It Only Leads to Arguments"... Chungnam's True Sentiments Hide Deeper After Martial Law](https://cwcontent.asiae.co.kr/asiaresize/304/2026051223490460082_1778597344.jpg)
