COVID-19 Spear Phishing, This Time a 'Cheonongye' Warning
Exploiting the Health Supplies Crisis Including Masks
Malicious Use Such as Embedding Attachments to Steal Information
[Asia Economy Reporter Lee Gwan-ju] Spear phishing exploiting the novel coronavirus disease (COVID-19) situation has emerged, requiring caution. The 'body temperature thermometer,' which is experiencing a shortage following masks, is the bait.
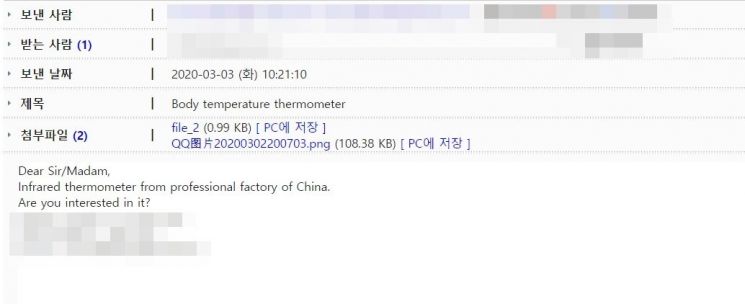
Recently, an email titled 'body temperature thermometer' was randomly distributed online. The sender's account was 'starlight-led,' which matches the internet address (URL) of a company located in Shenzhen, Guangdong Province, China. The email included a message saying, "Please contact us if you are interested in infrared thermometers," along with a photo of a non-contact thermometer and an attached file of unknown content.
This resembles a typical attachment form used in spear phishing. Upon checking the company's official website, it was confirmed that it is an LED lighting manufacturer unrelated to thermometers. There is no thermometer in their product catalog. It is presumed that someone impersonated the Chinese company to send spear phishing emails.
As COVID-19 rapidly spreads, a shortage of non-contact thermometers has occurred domestically. Demand has greatly increased at public offices and large supermarkets where many people enter and exit. Non-contact thermometers, which normally cost around 80,000 KRW, are currently being sold on internet shopping malls for 170,000 to 200,000 KRW. In this situation, emails of unknown origin pretending to be from Chinese companies selling non-contact thermometers are spreading.
If the attached file is executed, not only can the computer's information be stolen, but it can also be used as a channel for other related crimes later. It may also be 'GandCrab ransomware,' which encrypts files on the computer and demands virtual currency as a ransom to decrypt them.
Since the early stages of the COVID-19 situation, phishing emails aimed at stealing corporate information have been continuously distributed. Earlier last month, an email containing malicious code was spread, impersonating a Taiwanese manufacturer and using COVID-19 information sharing as bait. Domestically, emails impersonating the Korea Disease Control and Prevention Agency to lure victims to phishing sites to steal credit card information and passwords, as well as malicious email attacks presumed to be the work of the cyberattack group 'Kimsuky,' have been confirmed. The internet security industry explained that phishing emails in the form of corporate 'notices' have also been discovered, taking advantage of the increase in remote work due to COVID-19.
Hot Picks Today
 "If It's Uncomfortable, They Cut Ties": Three O...
"If It's Uncomfortable, They Cut Ties": Three O...
As the COVID-19 situation prolongs, related cybercrimes are expected to increase. Security company ESTsecurity stated, "Attempts to distribute malicious code by exploiting the public's curiosity and fear are increasing," and urged, "When receiving COVID-19-related emails from unknown sources, refrain from opening them and verify accurate information on official websites." The police also plan to strongly respond to COVID-19-related cybercrimes such as phishing emails and smishing messages.
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.