Possible Insider Involvement and Retail Store Collusion... KT Unauthorized Small Payment Scandal Widens
by Park Eugenie
by Lee Myeonghwan
Published 11 Sep.2025 11:05(KST)
Updated 11 Sep.2025 14:18(KST)
Damages So Far Reach 170 Million Won
Full Block on Femtocell Network Access Implemented
Payment Route Still Unidentified
Questions Remain Over Disabled Authentication Procedures

Ryu Jemyung, the 2nd Vice Minister of the Ministry of Science and ICT, is attending a briefing on September 10 at the Government Seoul Office in Jongno-gu, Seoul, regarding the KT unauthorized small payment breach incident. KT officials present are taking notes. 2025.9.10 Photo by Cho Yongjun
원본보기 아이콘The KT unauthorized small payment incident, which is believed to have involved the unprecedented method of "illegal micro base station (femtocell) hacking," is causing a growing stir as suspicions arise about possible insider involvement or connections to local dealerships.
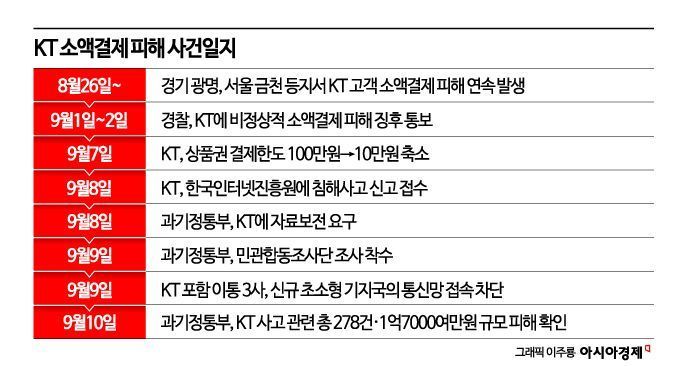
On September 10, the government announced that it had identified evidence of base stations accessing the KT network without registration, with the number of affected cases reaching 278 and the total damage amounting to approximately 170 million won. The government stated that a joint investigation team would be formed to uncover the details. The three major mobile carriers have completely blocked new femtocells from accessing their networks, but the exact route through which the payments were processed remains unknown. In particular, the key unresolved question is how an unregistered base station was able to connect to the carrier’s core network and facilitate small payments. Normally, multiple layers of key values and authentication procedures are required, but in this case, these processes were bypassed, allowing unauthorized small payments to be made.
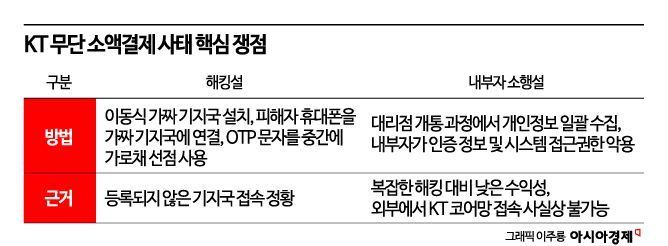
Scenario: Eavesdropping and Authentication Code Theft via Illegal Base Stations
Femtocells are small devices used to improve signal coverage in homes or offices. Typically, only devices registered with the carrier can connect to the network, but if an attacker installs an unregistered fake base station and lures devices to connect, all calls and messages from users are routed through that equipment.
Kim Youngdae, a professor at the School of Electrical Engineering at KAIST, suggested on social media that "it is possible the attacker modified a portable femtocell to intercept SMS authentication codes." Simply put, if an attacker hacks a femtocell device and attaches a battery and a small computer, it becomes a "mobile fake base station." When this device is powered on, nearby mobile phones mistake it for a legitimate base station and connect to it.
In this state, if a victim receives a one-time password (OTP) via SMS for a gift card purchase or similar transaction, the message is delivered not only to the phone but also to the hacked femtocell. A program embedded in the device then forwards the message directly to the attacker. The attacker simultaneously attempts an online payment, entering the stolen authentication code first. The victim receives the SMS as usual, but only discovers the fraudulent payment after the fact, upon reviewing their transaction history.
Yum Heungyeol, a professor in the Department of Information Security at Soonchunhyang University, explained, "If a femtocell is illegally connected to the network, attackers can eavesdrop on users' SMS messages or phone calls. Femtocells are supposed to undergo authentication when connecting to the network, but it appears that either the authentication process was bypassed or there was no such process at all."
Low Cost-Effectiveness Raises Questions About Motive... Possibility of Insider Involvement or Dealership Connections
However, considering the economics of the attack, the theory of a simple hacking operation is questionable. Lee Hyungtaek, CEO of Innotium, pointed out, "In most hacking cases, perpetrators quietly siphon off hundreds of millions of won. It is hard to understand why someone would choose the complex and easily detected method of base station hacking to steal only 170 million won."
He continued, "From a criminal efficiency standpoint, the cost-effectiveness is far too low. If this was indeed a hacking attempt, it may have been a demonstration by aspiring hackers, or possibly a test bed for a much larger cyberattack." He added, "If vulnerabilities in the network are identified and later exploited to simultaneously cripple electricity, finance, and telecommunications, it could escalate to a national crisis."
For these reasons, not all experts believe that hacking is the sole cause. A representative from a domestic security firm said, "The theory of theft via femtocell is just one hypothesis. In reality, the incident is characterized by the fact that victims were concentrated in specific local communities."
This representative explained, "Fake base stations typically target people in physical proximity at random, but in this case, many victims shared the same address or living area. This suggests the possibility that a local dealership processed the activation and authentication procedures for multiple users at once, which were then exploited." In fact, some dealerships have been criticized for security vulnerabilities due to the practice of handling everything from activation to app installation and authentication registration on behalf of customers who simply leave their ID cards. If personal information and authentication procedures were exposed in this process, it would be possible for such damage to occur even without the use of femtocell devices.
Lim Jongin, Distinguished Professor at Korea University's Graduate School of Information Security, also stated, "Only authenticated devices can connect to KT's core network. It is virtually impossible for an external hacker to obtain the necessary certificates and passwords to gain access." This is an aspect that KT has yet to explain. Professor Lim added, "If someone had that capability, they would have targeted tens of billions of won for a reasonable return on investment, so it is difficult to believe the operation ended with this level of damage."
Therefore, Professor Lim emphasized, "It is more likely that an employee of a partner company exploited internal controls rather than an external hacking attempt." He explained, "A partner company employee could have access to the authentication information for on-site equipment, and could temporarily deactivate existing devices to insert their own. If SMS authentication is manipulated in this process, stealing small payments is entirely possible."
He also pointed out, "The fact that KT failed to detect dozens of suspicious financial transactions is another problem. The failure of the Fraud Detection System (FDS) to function properly is evidence of a breakdown in internal controls."
The government has classified this incident as a major security breach and formed a joint public-private investigation team to determine the cause. Ryu Jemyung, the 2nd Vice Minister of the Ministry of Science and ICT, stated, "We will conduct a comprehensive inspection of the network management practices of the three major telecom companies and announce fundamental countermeasures soon."
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.