Only 'Initial Password' Exposed Personal Data of 297,000 People... LGU+ Had No Monitoring
by Kang Nahum
Published 27 Apr.2023 11:25(KST)
Updated 27 Apr.2023 16:17(KST)
Final Confirmation of Personal Data Leak of 297,117 Customers
Absence of Real-Time Monitoring, Control Systems, and Personnel
LG Uplus Ranks Last Among Top 3 Telecoms in Information Security Investment
The number of victims affected by the personal information leak at LG Uplus was finally confirmed to be 297,117. It was investigated that LG Uplus did not have an automated system capable of real-time monitoring and control during the period when personal information was being leaked. The government has decided to reorganize the cyber crisis prevention and response system, including establishing an ‘active cyber attack tracking system’ to prevent recurrence of such incidents.
"Hackers appear to have implanted malware using administrator accounts"
On the 27th, the Ministry of Science and ICT held a briefing at the Government Seoul Office and announced the 'Results of Cause Analysis and Countermeasures for the LG Uplus Breach Incident' containing these details.
Previously, the Ministry of Science and ICT and the Korea Internet & Security Agency (KISA) judged the massive leak of LG Uplus customer information as a serious breach incident and operated a ‘public-private joint investigation team’ including external experts from January 11. Later, this investigation team was reorganized into a ‘special investigation and inspection team’ and conducted investigations and inspections from February 6.
The inspection team removed duplicate data for the same individuals from the 600,000 leaked data records obtained from hackers by LG Uplus and confirmed data for a total of 296,477 individuals. Subsequently, they identified an additional 1,039 new customer information records not included in the original 600,000, confirming a total of 297,117 customers’ information was leaked.
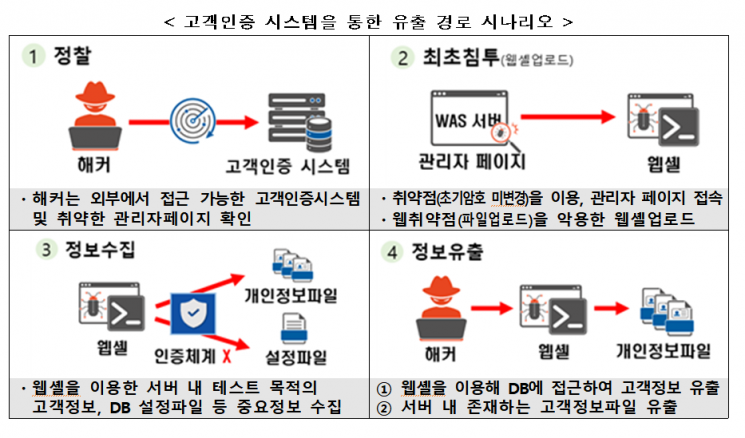
The inspection team pointed to the customer authentication database (DB) system as the leak route. Since June 2018, LG Uplus’s customer authentication DB system had the web administrator account password set to the system’s initial password, which allowed malware to be easily installed using the administrator account. The authentication system, including DB access control for administrators, was also insufficient, leading to the assumption that hackers could have used malware to exfiltrate files.
Despite large volumes of data containing customer information being leaked externally, LG Uplus was found to lack an automated system capable of real-time monitoring and control. There was no real-time monitoring system to detect and block abnormal signs such as large data transfers inside and outside the network. Additionally, the standards for log storage and retention periods for each system were irregular.
Absence of security equipment to detect and block DDoS attacks
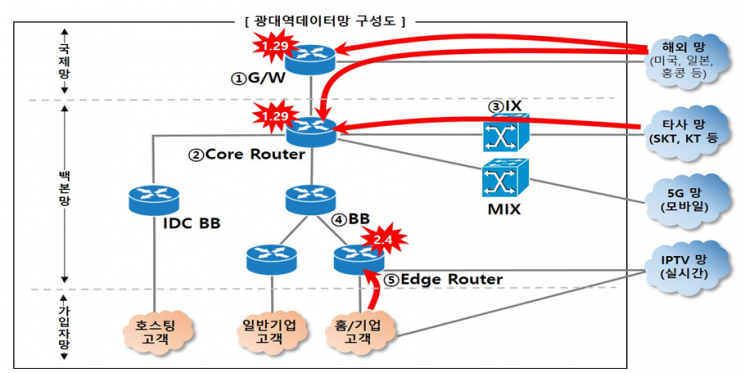
LG Uplus was helpless against DDoS attacks. Previously, five disruptions occurred in January and February to wired internet, VOD, and 070 phone services due to DDoS attacks on major routers (devices connecting different networks) of LG Uplus’s broadband data network.
The attackers targeted 14 major network devices (3 gateways and 11 routers) in the interconnection section (Internet eXchange) with other telecom companies for DDoS attacks. As a result, a large volume of abnormal packets flowed into the router devices, causing a sharp increase in CPU usage and system failures.
While other telecom companies minimize exposure of router information, LG Uplus had more than approximately 68 routers exposed externally before the DDoS attacks. Generally, access control policies (ACL, Access Control List) restrict communication types between routers, but LG Uplus’s security measures were insufficient. Furthermore, there were no intrusion detection and blocking security devices in each network segment, and an integrated management system for enterprise IT resources was also absent.
The inspection team pointed out the lack of professional security personnel and insufficient investment in information security related to LG Uplus’s successive incidents. There was a shortage of experts to protect core services and internal information, and the authority and responsibility of the information security organization were inadequate. In particular, IT and information security-related organizations were dispersed across multiple locations, making coordinated response and rapid decision-making difficult during emergencies.
Relatively low security investment compared to other telecom companies was also highlighted as a problem. According to the Ministry of Science and ICT’s data on 2022 information security investments of the three major telecom companies, KT invested the most with 102.1 billion KRW, followed by SK Telecom with 86 billion KRW. LG Uplus’s investment was the lowest at 29.2 billion KRW. Regarding information security personnel, KT and SK Telecom each had over 300 employees, whereas LG Uplus had only 91.
The Ministry of Science and ICT plans to reorganize the cyber crisis prevention and response system and promote related institutional improvements to prevent similar incidents in the telecom industry. The existing detection systems used for individual cyber threat responses will be integrated into a ‘Cyber Threat Integrated Detection System,’ and a system to detect and identify high-risk cyber threat target systems early will be established.
Additionally, an ‘active cyber attack tracking system’ will be introduced to select and track hacker groups operating against domestic companies, enabling cooperation with investigative agencies and others to respond before cyberattacks occur. Furthermore, legal amendments will be pursued to impose fines up to 20 million KRW on businesses that fail to report breach incidents.
A Ministry of Science and ICT official stated, "In preparation for increasingly diverse and expanding intelligent and organized cyber threats, we will strengthen the existing information security system into a more effective system and build a safe digital service powerhouse trusted by citizens and companies."
© The Asia Business Daily(www.asiae.co.kr). All rights reserved.